SAML 2.0
Overview
SmartIQ supports SAML 2.0 which is an open federation standard that allows an identity provider (IdP) to authenticate users and pass identity and security information between SmartIQ and other service providers (SP) enabling Single Sign-On (SSO) and Single Logout (SLO).
The diagram below shows how the SP-initiated SAML flow works.
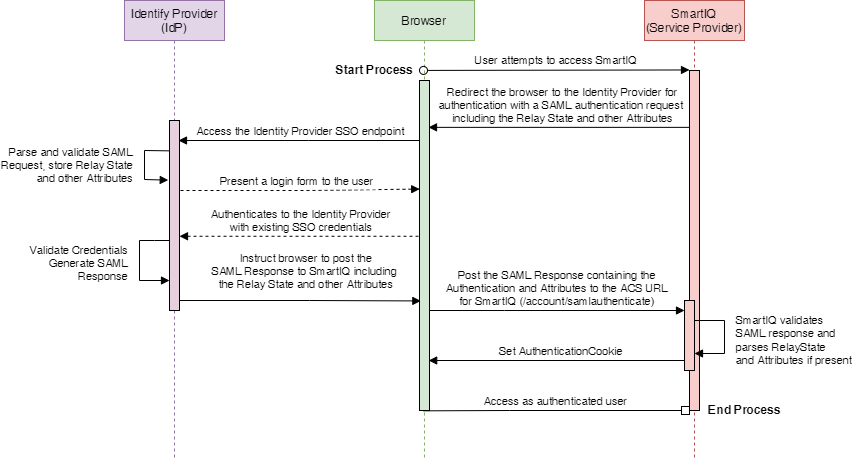
NoteSmartIQ supports both SP-initiated and IdP-initiated SAML flows. This means users can either login from the IdP login page and redirects to SmartIQ or users login from SmartIQ and redirects to the IdP page.
Single Sign-On (SSO)
SmartIQ supports the use of IdP for authentication to enable access without the need to re-key credentials when an existing session is present.
When a user attempts to log in, SmartIQ uses HTTP Redirect to pass an authentication request to the IdP. The IdP determines whether the user has already been authenticated or requires login. After login, the IdP sends an HTTP post binding back to SmartIQ with the status of the login and some additional metadata about the user.
Single Logout (SLO)
Typically, service providers use session cookies to keep sessions open when authenticated through an IdP for SSO. Once users logout of the IdP, most users assume that all sessions have been logged out. However, individual session cookies are valid until expired.
With SLO, when the user indicates they wish to logout, SmartIQ supports SAML Single Logout to completely close all sessions from all service providers.
Prerequisites
-
An existing SmartIQ environment installed with default Forms Authentication.
-
A SAML 2.0 provider with an Identity Provider (IdP) configured to:
- (Mandatory) Return a group membership as an assertion attribute (for example, IsMemberOf) to ensure that at least one user can be added to a SmartIQ Administrator Role after switching to SAML
- (Optional) Return profile information such as first and last name
Refer to your respective identity provider’s documentation for configuration settings. For example, Okta or Azure Active Directory.
- Identity Providers for both SmartIQ Manage and Produce whereby:
- The response is configured to be sent via HTTP-Redirect to:
https://yourserver/Manage/account/samlauthenticateorhttps://yourserver/Produce/account/samlauthenticaterespectively - The HTTP-Redirect or HTTP-POST response is signed.
- A meaningful name is given to the Service Providers (usually Produce and Manage)
- A certificate either installed on the SmartIQ web server or uploaded as file that can be used to check the SAML response signature (i.e. the certificate used by the IdP to sign the response).
- A user configured in the SAML 2.0 provider for testing that is a member of at least one known group.
- For single logout service, the Identity Provider should have the Single Logout Service response configured to be sent via HTTP-Redirect to:
https://yourserver/Manage/Account/SamlLogoutorhttps://yourserver/Produce/Account/SamlLogoutrespectively - Pass through of Relay State must be enabled in the Identity Provider if the use of deep links is desired.
- The response is configured to be sent via HTTP-Redirect to:
Terminology may vary among different Identity Providers, so check the Identity Provider documentation if you are not sure what values should be configured in SmartIQ and in the Identity Provider
SAML Authentication in Multi-Tenant Environments
To allow navigation to a specific tenancy and to authenticate using SAML instead of forms authentication:
-
When navigating to a specific form, SmartIQ is able to determine the tenancy of that form and will, therefore, use the authentication method defined by that tenancy.
-
A TenantId may be used to specify what tenancy to log in to if navigation to the Produce home page is required. The produce homepage in this situation will be the normal home page with
/b/<tenantid>appended to the URL.
For example, if Produce is normally https://IQtransform.com, then a specific tenancy can be navigated to at https://IQtransform/b/12345, where the tenant id is 12345.
Once a SAML Produce instance is navigated to, a cookie will be stored on that computer and will remember that SAML login is preferred when accessing that instance of SmartIQ. In this situation, in the unlikely situation where forms authentication is desired, the SAML tenancy must be logged out and cookies cleared.
SmartIQ Configuration
Step 1 - Identify a SAML Administrator Group
When the first user (usually a server administrator) attempts to access SmartIQ via SAML Authentication, SmartIQ needs to assign permissions to an External Group so they can access appropriate functions. If this step is not completed, user will not be able to administer anything post authentication.
Step 2 - Enable and Configure SAML
-
Open the SmartIQ Manage application and log in as an Administrator with Change settings permission.
-
Click Settings > SAML 2.0.
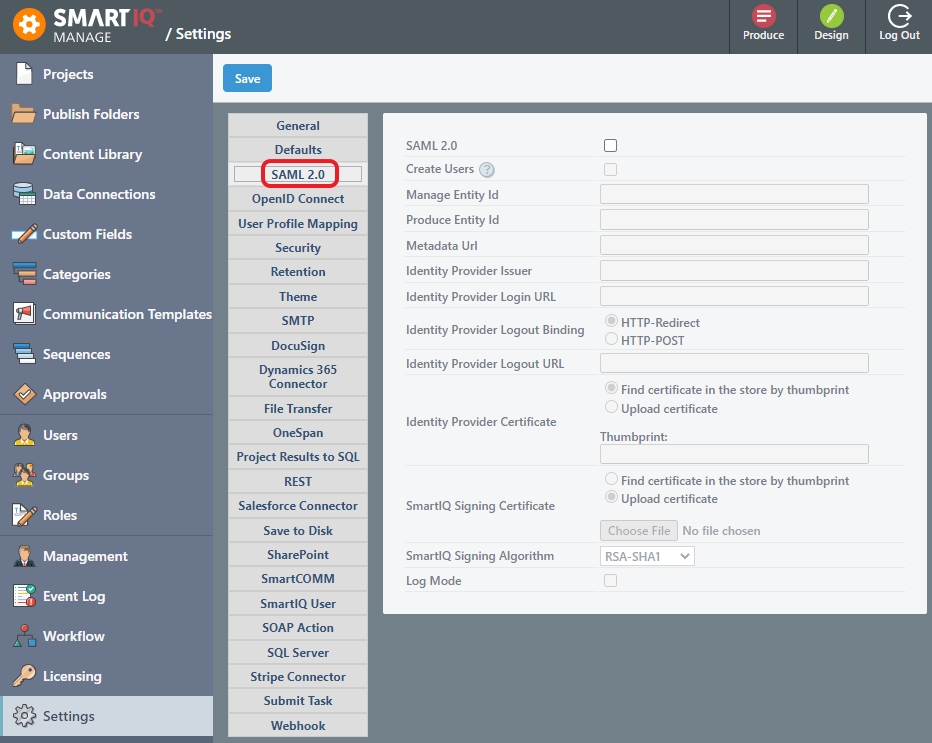
- Provide the necessary information. Refer to your Identity Provider's documentation for configuration and settings. For example: Okta or Azure Active Directory.
You can't have two apps in OKTA connected to SmartIQ SAMLOnly one OKTA app is valid per SmartIQ instance or SSO errors will occur. This means its not possible to redirect to both Manage and Produce separately.
Setting | Description |
|---|---|
SAML 2.0 | Provides the option to use SAML 2.0 |
Create Users | Provides the option to create a user in the SmartIQ platform. If unchecked, the user must already exist in SmartIQ to be able to login. |
Manage Entity Id (Mandatory) | The Entity Id of the Manage Service Provider. For example, |
Produce Entity Id (Mandatory) | The Entity Id of the Produce Service Provider. For example, |
Metadata URL | Enables reading information about the requirements of the service from this URL.
|
Identity Provider Issuer (Mandatory) | The Issuer ID of the Identity Provider. For example, |
Identity Provider Login URL (Mandatory) | The URL of the Single Sign on Service URL that SmartIQ will make the Redirect Request to. For example, |
Identity Provider Logout Binding (Mandatory) | Logout binding determines which binding will be used when a request is made. SmartIQ supports both REDIRECT and POST. The correct option is dependent on what your IDP is expecting. _ HTTP-Redirect (Default) – A Logout request using its signature to pass an authentication request element to the identity provider
|
Identity Provider Logout URL | The URL of the Single Sign Out Service in IDP that SmartIQ will make a logout request to. |
Identity Provider Certificate (Mandatory) | The certificate SmartIQ will use to check the signature received in the HTTP-Redirect Response. |
SmartIQ Signing Certificate (Mandatory) if Identity Provider Logout URL is provided. | The certificate SmartIQ will use to create the signature for the logout request. |
SmartIQ Signing Algorithm | Provides a selection of hashing methods for the SAML logout request to use with the above certificate. |
Log Mode | Enables capturing a more verbose description of all events during a SAML authentication (i.e. success and fail) that can be viewed in the Event Log. Useful for fault-finding new implementations. |
Last Failed SAML Login | Displays the last failed message, if logging has been turned on. |
OKTA
The Manage Entity Id and Produce Entity Id, this is the Audience URI (SP Entity Id). For Single Sign-Out, the entity ID should match the SP issuer in Okta if you are setting up SAML Login for Manage or Produce.
Give the Manage and Produce identity a unique value in SmartIQ Settings e.g. smartiq-produce and smartiq-manage. The Audience URI will then be smartiq.
You can only have one OKTA app per SmartIQ instance. Set up SSO just for Produce and SmartIQ will handle the redirect URL when a user tries to access other areas of SmartIQ. This implementation means users will always redirect to Produce first.
Step 3 - User Profile Mapping
As attributes specified in a SAML response are arbitrary, it is necessary to map particular user profile fields to the values provided in the SAML response.
-
Open the SmartIQ Manage application and log in as an Administrator with Change settings permission.
-
Click Settings > User Profile Mapping.
-
Provide at least the name of the attribute where the user’s Group Memberships are specified. Optionally specify any other user fields.
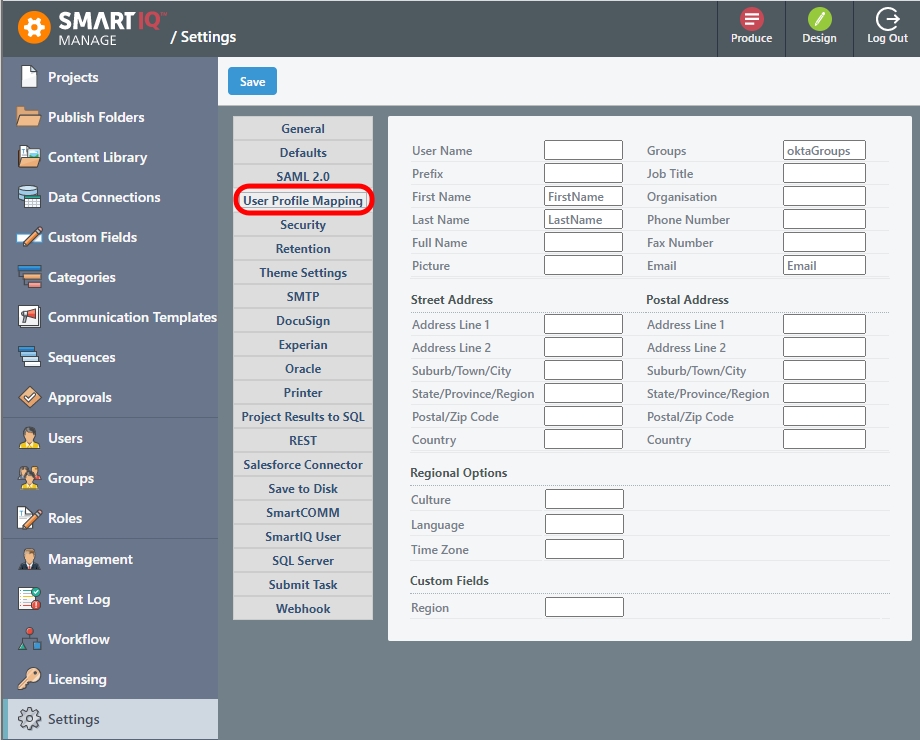
Available User Profile Mapping Fields:
Setting | Description |
|---|---|
User Name | A field to use for the SmartIQ Username if the default SAML ‘NameID’ element does not contain a meaningful value. This is a required field. For example, use the email address. |
Groups | The element to look for the user’s group Memberships. |
Prefix, Job Title, Organization, | Regular fields |
Culture | A culture code to use for example en-AU, zh-CN, es, etc |
Language | A language to use must be supported by SmartIQ. Possible values:
|
Time Zone | An appropriate user time zone. Possible Values:
|
- Click Save.
Step 4 - Test
-
Close all browsers to ensure any existing SmartIQ sessions are removed.
-
Open a new browser and navigate to SmartIQ Manage or Produce.
SmartIQ will create a SAML session as per the configured settings. If logging in for the first time, the Identity Provider's Login screen should appear or, if you already have an existing session, you should be redirected to the Produce or Manage Home page.
- Log out of SmartIQ Manage or Produce. You should be redirected to the Logout URL page.
Troubleshooting
There are a number of SAML browser inspections extensions (eg: SAML Chrome Panel etc) that can be used to trace the SAML flow and allow inspection of the requests and responses sent back and forth between the browser, SmartIQ and the Identity Provider.
We recommend the use of some sort of inspection tool if you are experiencing difficulties with SAML.
Updated 12 months ago
